New evidence uncovered by digital forensic experts supports the conclusion that the cyberattack on IPI in September was carried out in retaliation for our work in support of independent media in Hungary, IPI said today. These findings point to a widening campaign against Hungary’s independent media to include attacks on civil society organizations that voice support for them – even beyond Hungary’s borders.
An in-depth forensic analysis conducted by the Qurium, a non-profit based in Sweden, confirmed IPI’s initial assessment that the denial of service (DDoS) attack that brought down IPI’s website for several days this September was linked to a wave of cyber attacks on more than 40 Hungarian media sites last spring.
Specifically, Qurium’s analysis of log data from IPI and two other Hungarian news media showed that these attacks were connected and identified the infrastructures involved. Qurium said it was “highly probable” that the attacks on other Hungarian media, which included independent news sites as well as non-political magazines and outlets, were “carried out with this same attack infrastructure”.
The attack on IPI’s website came just days after we published a report on the cyberattacks on Hungarian media, calling the attacks a major new threat to the country’s independent media. At that time, an initial investigation of log data from the attack on IPI by our own IT teams found a message from the attacker, who also had left the same identifier in the log data of attacks on several Hungarian media.
Qurium’s investigation shows that the DDoS attacks on Hungarian media and IPI were operationalized through an established network of U.S.- and Europe-based service providers that are enabling – knowingly or unknowingly – the malicious use of their infrastructure to target independent media and civil society for commercial gain.
“This new analysis is a clear indication that the campaign against independent media in Hungary has escalated. This campaign has now gone transnational – and even civil society organizations beyond Hungary’s borders who stand in support of these important outlets can be targeted”, IPI Deputy Director Scott Griffen said.
Griffen added: “However, we must reiterate that for IPI, this incident has only strengthened our resolve. We will continue to stand strong with independent media in Hungary and will not be dissuaded by any attempts to disrupt our work.”
“We’re grateful to the team at Qurium for their important investigative work that has shed light on the attack network as well as the nature of the attacks on IPI and Hungarian media.”
Attacker remains elusive, but complex attack network revealed
Researchers at Qurium were unable to ascertain the actor or actors who were ultimately responsible for ordering the attack against IPI and other media outlets in Hungary. However, they were able to identify large parts of the attack network. As noted in our initial analysis, the attack was carried out with the use of internet services offered by multiple companies based in the US and Europe. Qurium dug deeper into the attack infrastructure to confirm that at least part of the cyberattack on IPI was carried out through the same network of proxy companies also involved in attacks against independent media outlets in Hungary.
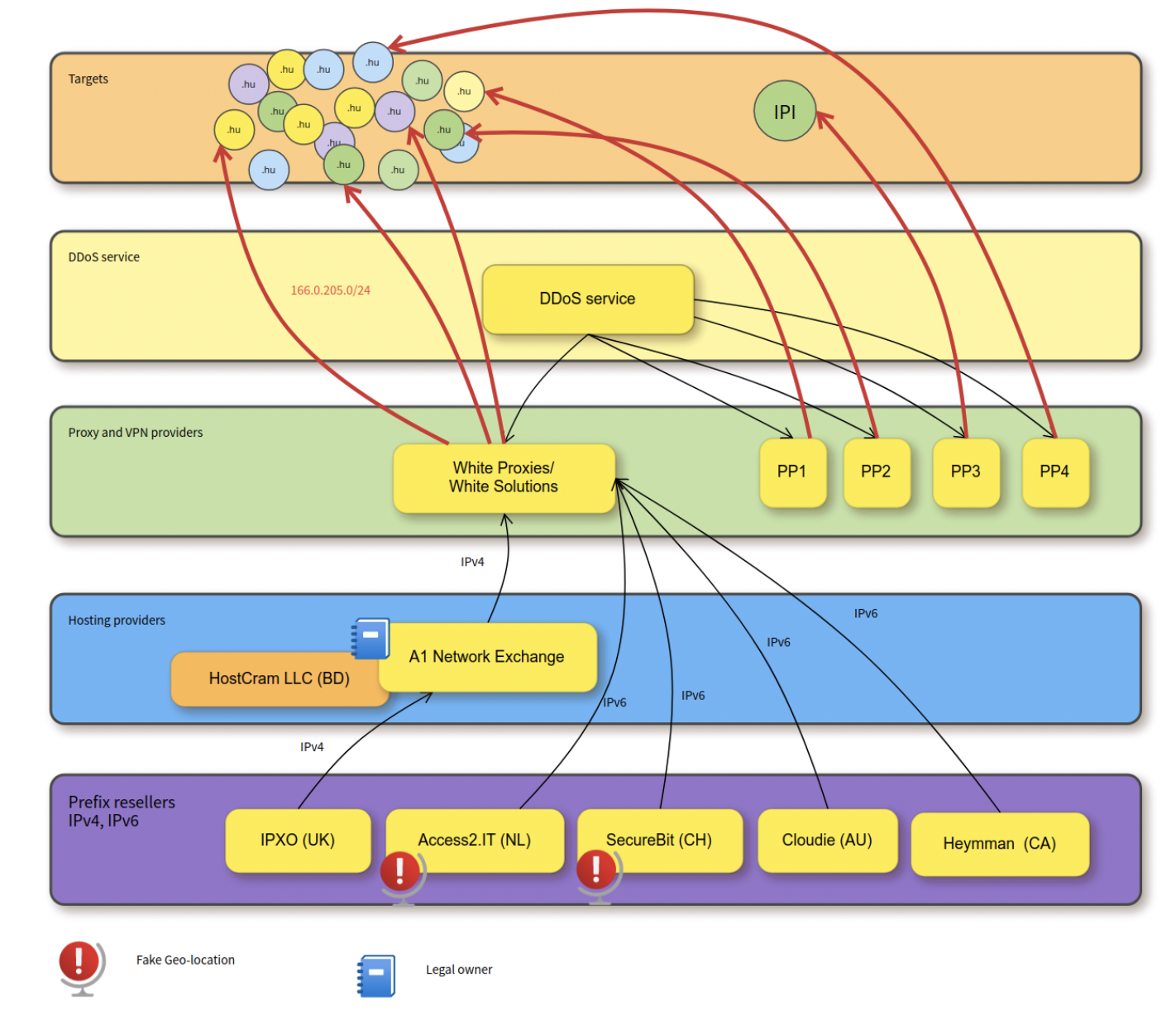
The above graphic illustrates the web of actors involved in the cyber attacks on IPI and Hungarian media, according to Qurium’s findings. It shows how different companies are needed to build the various parts of the infrastructure needed for these attacks. The forensic report revealed how a specific proxy provider that made use of several IP leasing services and hosting providers was ultimately used by the attacker to launch DDoS attacks. It also illustrates how difficult it is to track down the individual or individuals who are ultimately responsible for ordering the attack, as so many different layers are involved.
Qurium’s investigation identified a company called White Proxies (also known as White Solutions) as playing a central role in the attack. The company’s owners are not known. When contacted by Qurium, the company said it would implement mechanisms to prevent the events from recurring but then stopped communicating when Qurium asked for a point of contact or information on the company’s legal status.
Another company identified as being involved in the attacks is A1 Network Exchange, which is a hosting provider that leases IP networks to proxy providers. The owner of A1 Network is Shakib Khan, who is also connected with other companies that offer similar services, such as Etherdark Ltd, Intexon Ltd, and HostCram LLC, a company registered in Wyoming (US). Investigators at Qurium reached out to Khan to request information from him about who his client is, but he refused to divulge this information.
“Proxy providers like White Proxies and the companies profiting directly or indirectly from these type of services should do more to ensure that their services are not being used to carry out criminal activities,” Tord Lundström, forensic investigator at Qurium, said. “It’s too easy for these companies to evade responsibility – and this has to change.”
Digital attacks against journalists, civil society on the rise
Digital attacks are a growing threat to journalists, media, and civil society organizations around the world, as part of a broader campaign by individuals and governments to silence critics. These attacks come in the form of online harassment and threats, targeted surveillance, hacking, and cyberattacks – including denial of service attacks such as the one that targeted IPI and Hungarian media – aimed at silencing and censoring journalists and critics both within and beyond a country’s borders. Journalists covering corruption, crime, and war are often targets.
As Qurium’s report shows, there is a burgeoning illicit DDoS-for-hire industry of actors and companies offering their services to carry out types of attacks. DDoS attacks are relatively cheap – and can cost just a few hundred dollars – easy to execute, and exceptionally difficult to trace. This has made DDoS attacks a popular choice for cybercriminals – by some estimates DDoS attacks have jumped 40 percent in 2023 alone and have been launched against an increasingly diverse range of targets, including banks, schools, and hospitals.
According to information gathered by IPI, the DDoS attacks against Hungarian media have slowed in recent months, but not stopped. Both Media1 and Telex have experienced small attacks, which they were able to fend off with the help of more robust security tools offered through Cloudflare’s Project Galileo, which offers cybersecurity tools to at-risk organizations.
While these tools are often successful at deflecting malicious traffic and therefore keeping websites online, they require attention and adjustment, which in turn require additional resources and time. This highlights the urgent need for increased cybersecurity awareness, support, and resources for media organizations and civil society groups around the world.
